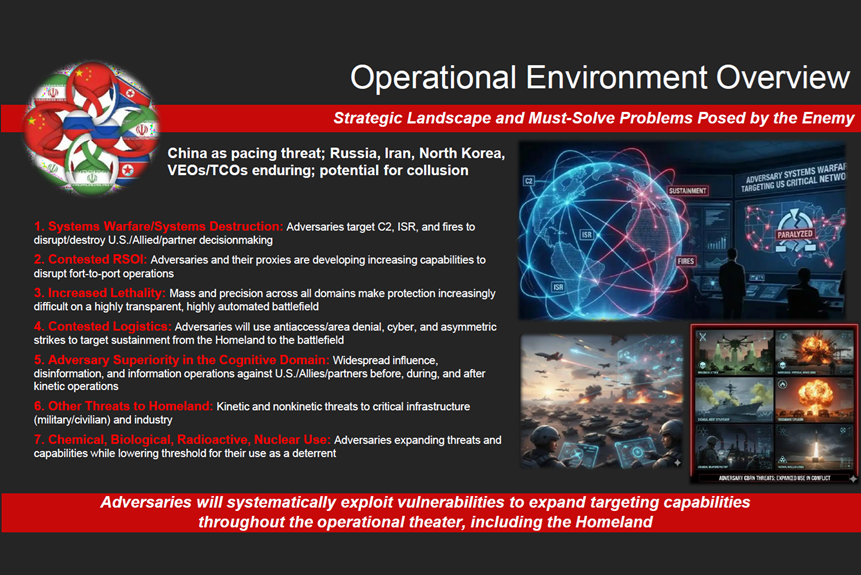
Operational Environment Must-Solve Problems Posed by the Enemy
By T2COM G-2
Distribution A: Approved for public release
File Size:
419 KB
File Type:
Page Count:
1
Share & Get The Message Out
Understanding the Modern Operational Environment and Strategic Adversary Threats
The current strategic landscape presents a complex operational environment defined by sophisticated and enduring threats. China, which is considered a pacing threat, along with Russia, Iran, North Korea, and non-state actors such as violent extremist organizations and transnational criminal organizations, pose significant, must-solve problems to the United States and its Allies and partner. These adversaries show a potential for collusion and will systematically exploit vulnerabilities to expand their targeting capabilities across the entire operational theater, including the U.S. Homeland. Understanding these challenges is critical for maintaining national security.
Key Problem One: Systems Warfare/Systems Destruction: Adversaries target C2, ISR, and fires to disrupt/destroy U.S./Allied/partner decisionmaking
Key Problem Two: Contested RSOI: Adversaries and their proxies are developing increasing capabilities to disrupt fort-to-port operations
Key Problem Three: Increased Lethality: Mass and precision across all domains make protection increasingly difficult on a highly transparent, highly automated battlefield
Key Problem Four: Contested Logistics: Adversaries will use antiaccess/area denial, cyber, and asymmetric strikes to target sustainment from the Homeland to the battlefield
Key Problem Five: Adversary Superiority in the Cognitive Domain: Widespread influence, disinformation, and information operations against U.S./Allies/partners before, during, and after kinetic operations
Key Problem Six: Other Threats to Homeland: Kinetic and nonkinetic threats to critical infrastructure (military/civilian) and industry
Key Problem Seven: Chemical, Biological, Radioactive, Nuclear Use: Adversaries expanding threats and capabilities while lowering threshold for their use as a deterrent
Keywords: operational environment, adversary threats, homeland, systems warfare, systems destruction, lethality, contested logistics, cognitive domain, CBRN, A2/AD, asymmetric warfare, disinformation, information operations, critical infrastructure, China, Russia, Iran, North Korea
Related Products
Fighting Through China’s Way of War and the Protection Challenge
Chinese and Russian Military Influence in Brazil
Exploiter Series: Sociocultural Exploitation
China’s Mobile Piers for Cross-Strait Operations Showcase PLA’s Innovation and Capability
Russia’s Armed Forces Regiment Attack on a Fortified Enemy Threat Template
Rising Russian Influence in the Sahel Spilling Over to Nigeria
Russia’s Armed Forces Regiment in a Positional Defense Threat Template
Russia’s Armed Forces Brigade Attack on a Fortified Enemy Threat Template
How China Fights Against a U.S. Army Division
Recent Spike in Lone-Actor Incidents Represents Most Likely Threat to T2COM